IT Security Diploma Level 3 + CyberSec First Responder: Threat Detection and Response
FREE PDF Certificate | Assessment Included | Tutor Support | 1 Year Access
Janets
Summary
- Certificate of completion - Free
Overview
With this combined training program, learn professional skills and gain core concepts of IT security & CyberSec and add value to your career. Learn from industry experts and get trained with everything you need to become a master in this sector just in days.
Improve your skills in IT Security and CyberSec at the same time with two most popular courses for the price of one.
The award winning IT Security Diploma Level 3 and CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations Online Training are our most popular online courses for anyone looking to start a career or gain skills in relevant industry. The IT Security Diploma Level 3 and CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations Online Training are taught entirely online by expert instructors. Modules are delivered through accessible, informative video lessons, online study materials, practical exercises, mock exams and multiple-choice assessments.
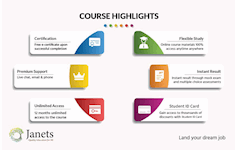
More key features of the courses:
- Earn free e-certificates upon successful completion of each course.
- Accessible, informative modules taught by expert instructors
- Study in your own time, at your own pace, through your computer tablet or mobile device
- Benefit from instant feedback through mock exams and multiple-choice assessments
- Get 24/7 help or advice from our email and live chat teams
Course media
Description
Course design
The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace.
You are taught through a combination of
- Video lessons
- Online study materials
- Mock exams
- Multiple-choice assessment
COURSE CURRICULUM
*IT Security Diploma Level 3*
Computer Fundamentals
- Basic Computer Terms
- Advanced Terms
- Networking Basics
- Basic Internet Concepts
- Internet Security
- Computers in the Workplace
- Tele-Commuting
- The Electronic World
Malware Protection
- Why You Need To Worry About “Malware”
- Viruses
- Spyware/Adware
- Safety & Security at the Browser Level
- Spyware Can Destroy
- How Does Spyware Spread?
- And much more....
*CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations Online Training*
Overview of Wireless Communications
- Identify the Importance of Risk Management
- Assess Risk
- Mitigate Risk
- Integrate Documentation into Risk Management
Analyzing the Threat Landscape
- Classify Threats and Threat Profiles
- Perform Ongoing Threat Research
- Resources that Aid in Research of Threats
Analyzing Recon Threats to Computing and Network Environments
- Implement Threat Modeling
- Assess the Impact of Reconnaissance Incidents
- Performing Reconnaissance on a Network
Analyzing Attacks on Computing and Network Environments
- Assess the Impact of System Hacking Attacks
- Cracking Passwords Using a Password File
- Assess the Impact of Web Based Attacks
- Assessing the Impact of Web-Based Threats
Analyzing Post-Attack Techniques
- Assess Command and Control Techniques
- Assessing Command and Control Techniques
- Assess Persistence Techniques
- Detecting Rootkits
- Assess Lateral Movement and Pivoting Techniques
Evaluating the Organization’s Security Posture
- Conduct Vulnerability Assessments
- Perform a Vulnerability Scan with Nessus
Collecting Cyber security Intelligence
- Deploy a Security Intelligence Collection and Analysis Platform
- Collect Data from Network Based Intelligence Sources
- Collecting Network-Based Security Intelligence
Analyzing Log Data
- Use Common Tools to Analyze Logs
- Analyzing Linux Logs for Security Intelligence
- Use SIEM Tools for Analysis
Performing Active Asset and Network Analysis
- Analyze Incidents with Windows-Based Tools
- Windows-Based Incident Analysis Tools
- Analyze Incidents with Linux Based Tools
- Linux Based Incident Analysis Tools
Responding to Cyber security Incidents
- Deploy an Incident Handling and Response Architecture
- Mitigate Incidents
- Hardening Windows Servers
Investigating Cyber security Incidents
- Apply a Forensic Investigation Plan
- Securely Collect and Analyze Electronic Evidence
- And much more....
Certification
Upon successful completion of the course, you will be able to obtain your course completion PDF certificate free of cost. Print copy by post is also available at an additional cost of £9.99
Questions and answers
hi can i get some course but i live in Turkey
Answer:Hi Sohrab, Good afternoon. The course is delivered through our online learning platform, accessible through any internet-connected device. Therefore, you can do the courses from anywhere in the world. Thanks
This was helpful.
Certificates
Certificate of completion
Digital certificate - Included
Reviews
Currently there are no reviews for this course. Be the first to leave a review.
Legal information
This course is advertised on reed.co.uk by the Course Provider, whose terms and conditions apply. Purchases are made directly from the Course Provider, and as such, content and materials are supplied by the Course Provider directly. Reed is acting as agent and not reseller in relation to this course. Reed's only responsibility is to facilitate your payment for the course. It is your responsibility to review and agree to the Course Provider's terms and conditions and satisfy yourself as to the suitability of the course you intend to purchase. Reed will not have any responsibility for the content of the course and/or associated materials.