Ethical Hacking - Ethical Hacking Training
New Year Sale: Pick Up a New Skill | Expert-Led CPD QS Course + Free PDF Certificate | Video Lessons | Tutor Support
Course Cloud
Summary
- Certificate of completion - Free
- Tutor is available to students
Overview
♧♧ Excel your career by enhancing Ethical Hacking skills with Course Cloud and get noticed by recruiters in this Hiring season! ♧♧
Worried about your future and looking for a way to develop your career? Course Cloud can be the best solution for you to succeed. Course Cloud makes home training easy, and Ethical Hacking Training Part-1 will teach you how to become a specialist without having to leave the comfort of your home. Ethical Hacking Training was designed in partnership with industry professionals and will add essential competencies to your resume. And if you enrol on Ethical Hacking now, you’ll get a special discounted price.
This bestselling Ethical Hacking Training Part-1 has been developed by industry professionals and has already been completed by hundreds of satisfied students. This in-depth Ethical Hacking Training Part-1 is suitable for anyone who wants to build their professional skill set and improve their expert knowledge.
The Ethical Hacking Training Part-1 is made up of several information-packed modules which break down each topic into bite-sized chunks to ensure you understand and retain everything you learn.
We know that you are busy and that time is precious, so we have designed the Ethical Hacking Training Part-1 to be completed at your own pace, whether that’s part-time or full-time. Get full Ethical Hacking course access upon registration and access the Ethical Hacking course materials from anywhere in the world, at any time, from any internet-enabled device.
Why would you choose Ethical Hacking course from Course Cloud:
- Get 5 premium Ethical Hacking courses at a single price
- Lifetime access to Ethical Hacking courses materials
- Full tutor support is available from Monday to Friday with the Ethical Hacking courses
- Learn Ethical Hacking skills at your own pace from the comfort of your home
- Gain a complete understanding of Ethical Hacking courses
- Accessible, informative video modules on Ethical Hacking taught by expert instructors
- Get 24/7 help or advice from our email and live chat teams with the Ethical Hacking bundle
- Study Ethical Hacking in your own time through your computer, tablet or mobile device.
- Improve your chance of gaining professional skills and better earning potential by completing the Ethical Hacking bundle
**** Additional GIFTS ****
- Free PDF Certificate
- Free 24/7 Tutor Support
- Lifetime Access To Ethical Hacking Course Materials From Anywhere
CPD
Course media
Description
Course Curriculum
Course Overview
- Ethical Hacking : Ethical Hacking - Course Overview
Building Your Virtual Lab Environment
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Creating a Virtual install of Kali using VirtualBox
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Installing the VirtualBox Extension Pack
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Creating a Virtual Install of CSI Linux
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Creating an Unattended Virtual Install of XP Using Virtualbox
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Taking a Snapshot of Your Current Configuration
Anonymity - Remaining Anonymous While Browsing Online
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Anonymize Kali Using Whonix
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Ensuring Anonymity Using the CSI Linux Gateway
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Assigning a Random MAC Address in Kali
Passive reconnaissance
- Ethical Hacking - Ethical Hacking - Lab-Information Gathering Using Maltego
- Ethical Hacking - Ethical Hacking - Lab-Conducting OSINT Using CSI Linux Investigator
- Ethical Hacking - Ethical Hacking - Using Metagoofil inside CSI Linux Analyst
Conducting a Passive Reconnaissance Using Shodan
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Preparing CSI Analyst to Use Shodan
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Using Shodan to Find Vulnerable Devices
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Using Shodan to Search for Vulnerable Databases
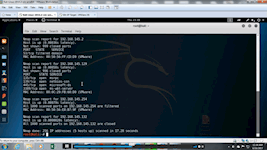
NMap
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Introduction to NMap
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-NMap Scripting Engine (NSE)
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Scanning for WannaCry Ransomware
Scanning for Vulnerabilities Using NESSUS
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Installing NESSUS Using Docker
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Scanning for Vulnerabilities Using Nessus
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Using Your Nessus Scan Results
Scanning for Vulnerabilities Using OpenVAS
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Installing OpenVAS Using Docker
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Scanning for Vulnerabilities Using OpenVAS
Exploiting Windows XP
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Video and Lab- Using Metasploit to Launch a DOS Attack Against Windows XP
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Establishing A VNC Shell Using Meterpreter
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Using Meterpreter to backdoor Windows XP
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab - Exploiting Vulnerable Applications on Windows XP SP2
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab - Hacking Windows XP via MS11-006 Windows Shell Graphics Processing
NetCat
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Creating a Virtual Install of Server 2008 Using virtualBox
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Create Reverse Shell Using MS09_050
Exploiting Linux
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Installing Metasploitable2 Using VirtualBox
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab - Learning to Hack Linux Using Metasploitable2
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab - Exploring Endpoint Attacks
Social Engineering
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Using the Social Engineering Toolkit (SET)
BASH Scripting for Pentesters
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Introduction to BASH Scripting
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Creating a BASH Script for Linux Fedora Part-1
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Creating a BASH Script for Linux Fedora Part-2
Password Cracking
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab – Password Cracking Using Medusa
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Passwords Cracking Using Mimikatz
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Password Cracking Using Hydra
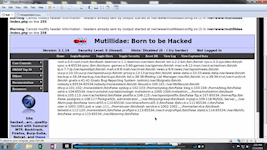
Web Based Application Attacks
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Installing w3af in Kali Linux Using Docker
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab – Conducting A Website Vulnerability Scan Using w3af
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab – Performing a Browser Based Attack
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-SQL Injection Attack Using SQLmap
Browser Exploitation Framework (BeEF)
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Configure Kali for Exploitation the WAN
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-The Browser Exploitation Framework (BeEF)
Capture the Flag Walkthrough - Mr. Robot
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab file - Capture the Flag (CTF) – Mr. Robot
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Video Walk Through -Key #1
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Video Walk through - Key #2
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Video Walk Through - Key #3
Capture the Flag Walkthrough – Stapler
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab File - Walkthrough - CTF – Stapler
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Capture the Flag - Stapler Part 1
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Capture the Flag - Stapler Part 2
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Capture the Flag - Stapler Part 3
Bonus - Digital Forensics Case Management
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Attaching an External USB Device in Kali
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab -Digital Forensics Using Autopsy Part I
- Ethical Hacking - Ethical Hacking - Ethical Hacking : Ethical Hacking - Lab-Digital Forensics Using Autopsy Part II
Certification
Once you have successfully completed the Ethical Hackingcourse, you will be awarded a PDF certificate for FREE as evidence of your achievement. The hardcopy certificate is £9.99.
Note: Delivery of the hardcopy certificates inside the UK is £4.99 each; international students have to pay a total of £14.99 to get a hardcopy certificate.
Who is this course for?
The Ethical Hacking course is primarily for motivated learners looking to add a new skill to their CV and stand head and shoulders above the competition. Anyone of any academic background can enrol on this Ethical Hacking course. However, this Ethical Hacking course is preferable for:
- Individuals interested in learning ethical hacking
- Individuals interested in learning how hackers hack computer systems
- Individuals interested in learning how to secure systems from hackers
Requirements
- Eagerness to learn Ethical Hacking.
- No prior knowledge is required to enrol on our Ethical Hacking Training
Career path
Anyone with an interest in Ethical Hacking will find our comprehensive course beneficial. Master the necessary skills to take a step closer to success with our Ethical Hacking bundle. Enhance your skills and explore opportunities such as —
- Security Engineer (£35K - £40K Per Annum)
- Network Security Engineer (£45K - £50K Per Annum)
- IT Security Engineer (£45K - £50K Per Annum)
And many more!
Questions and answers
Currently there are no Q&As for this course. Be the first to ask a question.
Certificates
Certificate of completion
Digital certificate - Included
Reviews
Currently there are no reviews for this course. Be the first to leave a review.
Legal information
This course is advertised on reed.co.uk by the Course Provider, whose terms and conditions apply. Purchases are made directly from the Course Provider, and as such, content and materials are supplied by the Course Provider directly. Reed is acting as agent and not reseller in relation to this course. Reed's only responsibility is to facilitate your payment for the course. It is your responsibility to review and agree to the Course Provider's terms and conditions and satisfy yourself as to the suitability of the course you intend to purchase. Reed will not have any responsibility for the content of the course and/or associated materials.